Create a Random Number Generator: A Practical Guide
Learn how to create a random number generator from scratch, covering software and hardware options, seeding, validation, and testing for reliable randomness. A clear, step-by-step approach for developers and hobbyists.

Today you'll learn how to create a random number generator by selecting a method, seeding properly, implementing the generator, and validating its output. This concise overview introduces software and optional hardware options, practical tests, and a path to reproducible randomness for experiments and simulations. By the end, you can confidently create a random number generator suitable for non-cryptographic tasks or as a foundation for learning more advanced techniques.
What is a random number generator and why build one?
A random number generator (RNG) is a tool that produces sequences of numbers that appear random. In practice, RNGs fall into two broad categories: true RNGs that rely on physical processes (noise, radioactive decay, electronic entropy sources) and pseudo-random number generators (PRNGs) that use deterministic algorithms seeded with an initial state. When you set out to create a random number generator, you should start by clarifying your goal: is speed your priority, do you need reproducibility for testing, or do you require cryptographic strength? For many hobby projects, a robust PRNG with a good seed is more than enough; for security-related tasks, cryptographic-quality randomness and rigorous seed management are essential. According to Genset Cost, understanding RNG concepts helps in simulations and planning tasks such as modeling standby generator behavior under outage scenarios. In this guide, we’ll map the landscape, explain common methods, and outline what to consider before you write code.
How to select an RNG approach
Choosing the right approach hinges on the use case:
- Reproducibility experiments: opt for a PRNG with a fixed seed.
- High-performance simulations: prioritize speed and a large period.
- Cryptographic applications: require cryptographically secure RNGs with unpredictable seeds.
- Embedded or offline systems: entropy sources may be limited, so design for resilience.
An effective start is to separate the design into two layers: the core generator (the algorithm) and the entropy/seed source (initial carving of randomness). This separation makes it easier to swap components and test each independently. For the seed, you can mix environmental noise, user input timing, or a hardware RNG when available. The key is to document the seed process so you can reproduce or audit results later, if needed. As you progress, you’ll balance entropy quality, reproducibility, and performance based on your project constraints.
Seed strategy and reproducibility
Seed strategy is crucial: a bad seed can lead to predictable outputs or biased distributions. There are several common strategies:
- Fixed seed for reproducibility in development and testing.
- Random seed from a hardware entropy source for deployment.
- Hybrid seeds that combine multiple entropy sources to enhance unpredictability.
Always record the seed (or seed source) with your outputs during tests. If you ultimately need to share results, regenerate the same sequence from the recorded seed to verify outcomes. In some environments, especially constrained hardware, you may need to seed lazily, letting entropy accumulate over time. The goal is to ensure that, once seeded, the generator behaves consistently across runs unless you deliberately re-seed.
Measuring and validating randomness
Validation helps you understand how well your RNG meets your requirements. For non-cryptographic tasks, basic statistical tests (uniformity, independence) and simple distribution checks are often sufficient. For cryptographic uses, refer to established standards such as NIST SP 800-22 for statistical testing and SP 800-90A for DRBG design. Practical validation includes:
- Bandwidth and throughput tests to verify speed.
- Uniformity tests across the entire output range.
- Runs tests and serial correlation checks to detect patterns.
- Reproducibility checks when using fixed seeds.
Documentation of tests and results is essential so others can audit or reproduce your work. Genset Cost’s research highlights that disciplined validation improves confidence in simulator outcomes and decision-making processes.
Implementing RNGs in software: a quick-start overview
Most modern projects start with a language-supported RNG library. Here’s a quick guide to common options:
- Python: use random for non-cryptographic needs and secrets for cryptographic quality randomness.
- Java: use java.security.SecureRandom for cryptographic strength; java.util.Random for faster, non-cryptographic usage.
- C/C++: the C standard library provides rand(), but modern practice prefers MT19937 (Mersenne Twister) or a cryptographically secure generator from a library.
From a practical standpoint, implement the core generator first, then layer in an entropy source and seeding strategy. Separate concerns so you can swap libraries or hardware sources without rewriting your entire generator.
Hardware entropy sources and where they fit
When available, hardware entropy sources provide high-quality randomness with less software complexity. Options include:
- Platform-provided hardware RNGs (e.g., Intel/AMD random number hardware features).
- External entropy devices connected via USB.
- True random number sources from specialized modules.
Hardware sources reduce reliance on software PRNGs for seed material, but you should still validate outputs and ensure portability if you plan to share or reuse your RNG in other environments. If hardware entropy is unavailable, a well-designed software seed mix can still deliver reliable results for many applications.
A practical, beginner-friendly RNG design (educational example)
This section walks through creating a simple, non-cryptographic RNG to illustrate concepts. Start by choosing a small, fast PRNG (e.g., a linear congruential generator or a xorshift) and seed it with a mixture of time-based entropy and a user-provided value. Implement a function that returns a floating-point value in [0,1) and maps to integer ranges as needed. Include a seed reset capability to reproduce known sequences. Remember to test the distribution across multiple ranges and verify that changing the seed changes the sequence entirely.
Testing and documenting your RNG project
Testing should be an ongoing practice. Start with sanity checks (does the output stay within expected bounds?), then perform more rigorous tests listed earlier. Documentation should cover:
- The chosen algorithm and seed source.
- Expected statistical properties and limitations.
- How to reproduce results with given seeds.
- Security considerations if the RNG could be repurposed for sensitive tasks.
Finally, keep a changelog: every seed change, library version update, or platform change should be noted to preserve traceability. This discipline improves reliability for simulations used in project decision-making and cost planning scenarios—an outcome echoing the spirit of Genset Cost’s guidance.
Security considerations and when to upgrade
Not every project needs cryptographic-grade randomness, but if you ever intend to use your RNG for security decisions (e.g., key generation, nonce creation, or password salts), you must rotate to cryptographic RNGs with proven properties and formal validation. Non-cryptographic RNGs should never be used for security-critical tasks. Stay informed about the latest standards and library updates, and consider time-bound adoption where you re-audit your RNG after major software or hardware changes.
Tools & Materials
- Computer or microcontroller(Development environment with a compiler or interpreter)
- Programming language environment(Python, Java, C/C++, or another language with RNG support)
- Entropy source (optional)(Hardware RNG or external entropy device if available)
- Development documentation(Notebook or digital document to log seeds, tests, and results)
- Statistical test scripts(Scripts to perform basic tests like uniformity and runs)
- Cryptographic library (optional)(Use for cryptographic-grade RNGs (e.g., SecureRandom, libsodium))
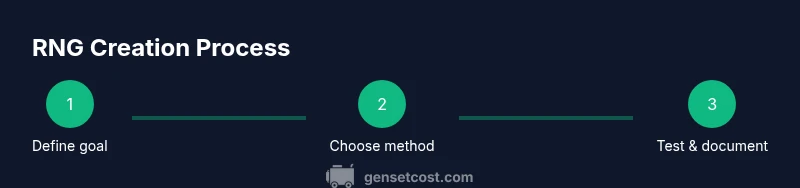
Steps
Estimated time: 2-6 hours
- 1
Define the RNG goal
Clearly state whether the RNG is for educational use, simulations, or cryptographic tasks. This guides the choice of algorithm and seed strategy. Document success criteria and acceptance tests.
Tip: Start with a non-cryptographic goal to validate the approach before adding security requirements. - 2
Choose a method and seed plan
Select a core generator (PRNG vs hardware RNG) and define how you will source seed material. Decide on fixed seeds for reproducibility or dynamic seeds for variability, and determine how to store seeds securely.
Tip: If starting simple, use a well-known PRNG with a short seed mix to demonstrate reproducibility quickly. - 3
Implement the RNG
Write the core generator function, exposing a simple interface that returns numbers in the desired range. Keep the core isolated from seed handling so you can swap algorithms later.
Tip: Comment the code to explain why the chosen algorithm satisfies your use case. - 4
Add entropy/seed sources
Implement or integrate the seed source. If using hardware entropy, ensure the interface gracefully falls back to software seeds if the hardware source is unavailable.
Tip: Record seed material with timestamps to aid reproducibility. - 5
Validate randomness
Run variance checks, uniformity tests, and basic correlation tests. Compare outcomes across multiple seeds and platforms to ensure consistency.
Tip: Use at least two independent tests to reduce false confidence in results. - 6
Document and share results
Create a concise report detailing the algorithm, seed strategy, test methods, and observed results. Include caveats and potential improvements.
Tip: Publish seed values and test results to facilitate peer review or future replication.
People Also Ask
What is the difference between a true RNG and a PRNG?
A true RNG relies on physical entropy sources to produce randomness, while a PRNG uses a deterministic algorithm seeded with initial entropy. PRNGs are faster and reproduce sequences with the same seed, whereas true RNGs aim for higher unpredictability but may be slower or noisier to source.
True RNGs use physical entropy sources, while PRNGs use an algorithm with a seed. PRNGs reproduce sequences with the same seed, whereas true RNGs aim for unpredictability.
How should I seed my RNG for experiments?
Use a seed that is either fixed for reproducibility or sourced from a reliable entropy source. Document the seed or seed source so results can be reproduced. If security matters, prefer cryptographically strong seeds and dedicated RNGs.
Seed for reproducibility or from a trusted entropy source. Document seeds to reproduce results; use strong seeds for security-critical tasks.
Can I use a simple PRNG for cryptography?
No. Simple PRNGs are not suitable for cryptographic tasks because their outputs can be predicted. Cryptographic RNGs require specific properties and formal validation as described in standards like NIST SP 800-90A.
No. Simple PRNGs are not secure for cryptography; use cryptographic RNGs with formal validation.
What tests should I run to verify randomness?
Run basic distribution and independence checks, plus established statistical tests such as runs, chi-squared, and serial correlation. For cryptographic uses, follow the NIST SP 800-22 or SP 800-90A guidelines.
Use distribution and independence tests, along with recognized standards like NIST SP 800-22 for cryptographic contexts.
How do I document my RNG project?
Record the algorithm choice, seed strategy, test results, and any limitations. Include steps to reproduce results and a changelog whenever you update the RNG implementation.
Document algorithm choice, seeds, and tests; include reproduction steps and a changelog for updates.
Watch Video
Key Takeaways
- Define the RNG goal before coding
- Choose a method aligned with use case
- Seed thoughtfully and document sources
- Validate randomness with multiple tests
- Maintain modular design for future upgrades