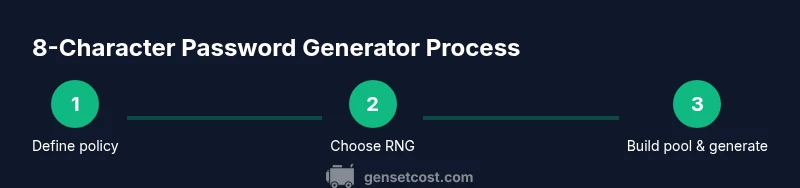
8 Character Password Generator: Step-By-Step Guide
Learn how to build a secure 8 character password generator. This guide covers entropy, character sets, implementation options, testing, and best practices for a compact yet strong password tool.
This guide shows you how to construct an 8 character password generator that uses cryptographic randomness and a diverse character set. You’ll define policy, build a secure pool, implement the generator in your preferred language, and validate the output. Follow these steps to produce reliable, short-but-strong passwords.
Why an 8 character password generator matters for everyday security
In today’s digital landscape, a compact tool like an 8 character password generator can help users create passwords that are short enough to memorize in some contexts yet still resistant to common attacks when designed properly. This article treats the topic with the care you’d give to a backup power plan: plan for reliability, randomness, and repeatability. According to Genset Cost, security habits should be as deliberate as home electrical planning, because a weak password can undermine even the best hardware protections. By focusing on an 8 character password generator that leverages cryptographic randomness and a diverse character set, you can balance usability with security. We’ll explore policy, implementation options, testing, and practical UX considerations so homeowners and property managers can deploy a dependable tool for everyday routines.
Throughout this section and the following ones, you’ll see how the same disciplined approach used in sizing and installation workflows applies to password generation. A strong password generator doesn’t rely on guesswork; it relies on a principled design that respects entropy, randomness, and secure storage practices. The goal is to produce passwords that are not predictable, while staying concise enough to fit tight form fields, clipboard workflows, and onboarding sequences. The 8 character constraint should be treated as a boundary that informs your character pool, RNG choice, and validation tests.
For practitioners and decision makers, building an 8 character password generator also serves as a practical demonstration of cryptographic hygiene and user experience design. The lessons here translate to other security tools you might deploy in a home or property-management context, such as access portals, guest Wi‑Fi credentials, or one-time codes. The emphasis is on reproducibility, auditable randomness, and clear guidance for users who need to generate passwords quickly under time pressure.
wordCountOnlyBlockTip
Tools & Materials
- Computer with a modern OS(Windows/macOS/Linux. Needed to run scripts or code samples.)
- Text editor or IDE(VS Code, Sublime Text, or similar for editing scripts.)
- Python 3.x or Node.js(Choose one runtime to implement the generator.)
- Cryptographically secure RNG(Use secrets (Python) or crypto.getRandomValues (JS) for randomness.)
- Documentation for password policy(Reference guidelines on required character classes if you’re integrating with policy.)
- Clipboard utility(Optional: streamline copying generated passwords to the clipboard.)
Steps
Estimated time: 15-25 minutes
- 1
Define 8-character policy
Decide that the password length is exactly 8 and determine which character classes to include (uppercase, lowercase, digits, and symbols). This policy will shape the pool of available characters and the randomness requirements.
Tip: Document the policy so users know what is allowed and why the length is fixed at 8. - 2
Choose a cryptographically secure RNG
Select a randomness source that resists predictability, such as Python’s secrets module or the Web Crypto API in JavaScript. A secure RNG is essential for an 8 character password generator to avoid patterns.
Tip: Avoid Math.random() for security-critical password generation. - 3
Assemble the character pool
Create a pool combining uppercase letters, lowercase letters, digits, and symbols as required by policy. The pool should be large enough to prevent easily guessable sequences while keeping length fixed at 8.
Tip: Include at least three distinct character classes to maximize entropy per character. - 4
Generate the 8 characters
Randomly select 8 characters from the pool using the cryptographic RNG. Ensure the loop uses a uniform distribution across positions to avoid bias.
Tip: Avoid reusing positions or dependencies between selections that could reduce randomness. - 5
Validate output and edge cases
Run multiple iterations to verify the distribution of characters and that every password adheres to policy. Check for accidental patterns or repeated sequences.
Tip: Automate a simple entropy check and length verification as part of unit tests. - 6
Document usage and security notes
Provide clear guidance on when to use the generator, how to store passwords securely, and why 8-character constraints matter in specific contexts.
Tip: Encourage users to use the generator only for temporary credentials in controlled environments.
People Also Ask
What is an 8 character password generator?
An 8 character password generator is a tool that creates passwords exactly eight characters long using a cryptographically secure RNG and a defined character set. It helps balance memorability with security by avoiding obvious patterns.
An eight-character password generator creates short, secure passwords using proper randomness and a defined character pool.
How strong is an 8 character password?
Strength depends on the character set and randomness. If you include at least three classes (uppercase, lowercase, digits, symbols) and use a cryptographic RNG, an eight-character password can be resistant to common guessing within practical limits.
With a strong character mix and true randomness, an eight-character password can be reasonably secure for many everyday tasks.
Can I reuse passwords generated by this tool?
No. Treat each generated password as unique to reduce cross-site risk. If you must reuse, apply separate salts and two-factor authentication where possible.
Try not to reuse passwords. If you must, pair with extra protections like two-factor authentication.
Should symbols be required in the 8-character password?
Including symbols increases complexity and resistance to brute-force attacks. If the policy allows, include symbols alongside letters and digits.
Yes—symbols help harden the password, as long as your system accepts them.
Is it safe to copy passwords to the clipboard?
Clipboard traffic can be intercepted by other apps. Use short-lived clipboard access, clear the clipboard after use, and consider alternative paste flows when possible.
Be careful with clipboard use; clear it after pasting and restrict access if you can.
What are common pitfalls when implementing an 8-character generator?
Bias in RNG, biased character pools, and overlooking edge cases in validation are common pitfalls. Rely on established libraries and include unit tests.
Watch out for RNG bias and ensure your tests cover edge cases.
Watch Video
Key Takeaways
- Define exact length and character-class policy before coding.
- Use a cryptographically secure RNG for true randomness.
- Ensure the pool includes at least three character classes for stronger entropy.
- Validate outputs with tests and simple entropy checks.
- Document usage, security considerations, and limitations.